Phase 2 HIPAA Audits: What to Expect from Your Business Associates
April 21, 2016
Last month, the Department of Health and Human Services’ Office for Civil Rights (OCR) launched the phase 2 of HIPAA Audit Program. The second phase of the audit will now focus on whether covered entities and business associates adhere to the HIPAA Privacy, Security, and Breach Notification Rules. If your business associates are handling electronic Protected Health Information (PHI), you must ensure your partners have proper HIPAA safeguards in place.
Ignorance of HIPAA requirements is not an excuse for violating the rules. An annual maximum of $1.5 million per violation can be charged for noncompliance.
In light of the phase 2 audits, here’s a list of important requirements to verify with your business associates:
1. PHI Handling Meets Current Audit Protocol Requirements
Under Section §164.306(a) of the OCR Current Audit Protocol, covered entities and business associates must ensure confidentiality, integrity and availability of PHI; protect against reasonably anticipated threats or hazards to the security or integrity of PHI; protect against reasonably anticipated uses or disclosures of PHI that are not permitted or required by the Privacy Rule; and ensure compliance with Security Rule by its workforce.
Quick Fact: An insurance holding company in Puerto Rico agreed to pay a $3.5 million settlement for multiple breaches and violations involving unsecured PHI.
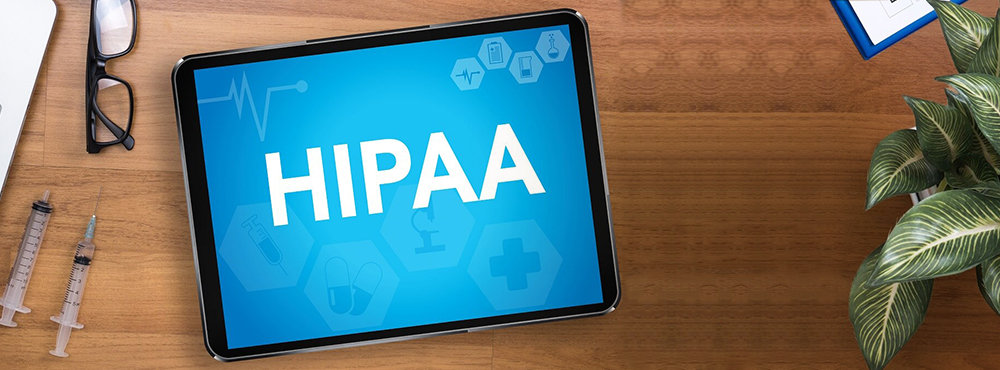
2. Data is Encrypted in Transit and at Rest
The OCR imposes that PHI data must be unusable, unreadable, or indecipherable by an unauthorized user. The HIPAA Security Rule Data defines data encryption as the use of an algorithmic process to transform data into a form in which there is a low probability of assigning meaning without use of a confidential process or key.
Due to the prevailing cases of data breach, Section §164.312(a)(2)(iv) and §164.312(e)(2)(ii) require that PHI data is encrypted to ensure confidentiality and integrity of the data. Two encryption methods should be applied:
- Data Encryption In Transit:
“Data in transit” is data being accessed over a wireless network or a cable network. Data in transit moves across untrusted networks such as the internet or through private networks such as corporate Local Area Networks (LANs). - Data Encryption At Rest:
“Data at rest” is inactive data stored on a physical media (e.g. servers, spreadsheets, mobile devices). Data at rest includes but not limited to corporate files stored in a user’s computer hard drive, data stored in secure online database servers, or files on an offsite storage location.
Quick Fact: A medical research firm in New York agreed to pay a $3.9 million settlement after an unencrypted laptop was stolen from an employee’s car.
3. Audit Logs are Tracked and Stored
Audit logs record various activities and events taking place on an end user device or in an information system. Section §164.312(b) requires that audit logs are recorded for all activities accessing PHI, such as the identity of the authenticated user, what information was accessed by the user, what PHI was viewed or changed and by whom. In addition, Section §164.316(b)(2)(i) requires that the audit logs are stored for six years.
Quick Fact: One of the nation’s largest healthcare companies agreed to pay a $1.7 million settlement for the lack of technical safeguards to authorize access to PHI in its online database applications.
4. A Signed Business Associate Agreement is in Place
Section §164.314(a)(1) requires that the entity must have policies and procedures in place regarding its contractual arrangements with vendors or other entities to which it discloses PHI for use on its behalf.
A business associate agreement holds parties liable for failing to safeguard PHI in accordance with the HIPAA Security Rule and is subject to civil penalties. The contract between the entity and its associates defines and limits the permitted use and disclosure of PHI by the business associate. In phase 2 of the HIPAA Audit Program, the OCR is collecting the contact information of covered entities and business associates for inclusion in potential audit pools.
Quick Fact: A hospital in Minnesota agreed to pay a $1.5 million settlement for failure to implement a business associate agreement with its vendor.
Resources for the Phase 2 HIPAA Audit
For more information on the phase 2 of the HIPAA Audit Program, the following resources are available from the U.S. Department of Health and Human Services:
- Current HIPAA Audit Protocol
- Audit Pre-Screening Questionnaire
- Sample Template for Business Associate Listing
Caspio’s HIPAA-Compliant Platform
Since the launch of the Caspio HIPAA Edition in 2014, Caspio continues to serve as a strategic technology partner for healthcare organizations relying on its HIPAA-compliant application platform. Users of the HIPAA Edition include state and local government agencies, large insurance providers, state insurance exchanges, hospitals, research universities, and pharmaceutical companies.
“The healthcare industry is facing increasing pressure and scrutiny, and Caspio is prepared to support our customers as a trusted technology partner,” said Frank Zamani, Founder and CEO of Caspio. “We have invested a substantial amount of time and resources to ensure our platform and operations are HIPAA-compliant and we are proud to be the leading HIPAA-compliant platform meeting this demand across the healthcare industry.”
To learn more about Caspio’s HIPAA Edition, request a free consultation with a product expert.